- Posted
- Operational Technology (OT) Security
The Air-Gap Dilemma: Why True OT Resilience Requires On-Premises Testing
The most sensitive operational technology environments in the United States—nuclear facilities, water treatment plants, defense installations, and power grids—remain deliberately isolated from the internet for good reason. Air gaps and unidirectional gateways (data diodes) exist because the consequences of compromise aren’t measured in lost revenue or reputational damage, but in public safety and national security.
Yet this very isolation creates a testing paradox. How do you validate your security controls, train your defenders, and stress-test incident response when your most critical systems are physically separated from the outside world—and need to stay that way?
A Threat Landscape That Demands Realistic Testing
Nation-state actors are targeting U.S. critical infrastructure with increasing sophistication and patience. In February 2024, CISA, NSA, and the FBI issued a joint advisory warning that Volt Typhoon—a PRC state-sponsored threat group—had compromised IT environments across communications, energy, transportation, and water systems. FBI Director Christopher Wray characterized the campaign as “the defining threat of our generation.”
What makes Volt Typhoon particularly concerning is their objective. According to the joint advisory, the group’s targeting and behavior is “not consistent with traditional cyber espionage or intelligence gathering operations.” Instead, they are pre-positioning themselves on IT networks to enable lateral movement to OT assets—establishing persistent access that, in some cases, has remained undetected for five years or longer.
These actors aren’t interested in immediate disruption. They’re building capabilities to disable critical communications and infrastructure during a future geopolitical crisis. And their tradecraft—living off the land using built-in system tools, avoiding malware that triggers EDR alerts—makes detection extraordinarily difficult.
Gartner’s 2025 Hype Cycle for Cyber-Physical Systems Security notes that cyber events in OT environments have increased year over year, with impact ranging “from mere annoyance to hundreds of millions of dollars in lost revenue, along with reliability, life, and safety impacts.”
The Limits of Cloud-Based Testing
For many industries, cloud-based security platforms offer flexibility and convenience.
But for organizations operating behind air gaps and data diodes, cloud dependency creates unacceptable risk.
The data sovereignty problem: Network topology data, vulnerability assessments, and security control configurations for facilities like nuclear plants or defense installations aren’t just sensitive—they’re matters of national security. Uploading this information to any cloud environment, regardless of compliance certifications, creates a new attack vector that didn’t exist before. The schematic of a water treatment facility’s SCADA network or the firmware signatures of a power grid’s protective relays should never traverse the public internet.
Respecting the diode: Unidirectional gateways exist specifically to ensure that data can flow out of a secure network for monitoring purposes, but nothing can flow back in. According to Gartner, these hardware-based appliances allow data to travel in only one direction. “As it’s physically impossible for data to travel in the wrong direction, there’s no risk of misconfiguration or exploitation of vulnerabilities.” Cloud-based testing platforms cannot operate within these constraints without fundamentally compromising the security architecture they’re supposed to validate. Testing behind the fence line requires solutions that respect—rather than work around—these physical boundaries.
The virtualization ceiling: The most sophisticated OT attacks don’t just target software. They exploit the physical behaviors of hardware—the specific timing characteristics of a programmable logic controller (PLC), the electrical signatures of a safety system, the precise firmware running on a particular model of controller. Stuxnet demonstrated this in 2010, when it targeted Siemens Step7 software and S7 PLCs to manipulate centrifuge speeds in Iran’s nuclear program, ultimately causing physical destruction while operators saw only normal readings on their screens. Purely virtualized testing environments can simulate protocols like Modbus and DNP3, but they cannot replicate how a real Allen-Bradley PLC or a Schneider safety relay actually responds under attack conditions.
Moving Beyond Tabletop Exercises
Regulatory pressure compounds the operational challenge. Frameworks like NERC CIP for the energy sector and the IAEA’s cybersecurity guidance for nuclear facilities increasingly emphasize not just policy documentation but demonstrated capability. SEC 8-K disclosure requirements mean organizations must be able to assess the material impact of cyber incidents quickly and accurately—something tabletop exercises alone cannot validate.
Traditional security measures including basic tabletop exercises are insufficient for addressing the complexities and unique vulnerabilities associated with critical infrastructure. Organizations need to stress-test controls, validate incident response strategies, and prove to regulators and boards that their defenses can withstand realistic attack scenarios.
The challenge: doing this without exposing classified network data, compromising air-gapped architectures, or training defenders on generic simulations that bear little resemblance to their actual environment.
A Realism-Based Approach to OT Testing
Addressing this gap requires rethinking how testing platforms are deployed and the level of realism they actually provide. SimSpace has developed a layered approach specifically designed for organizations that cannot—or should not—rely on cloud infrastructure for security validation.
The model operates across four layers of increasing realism:
- Layer 1 (Virtualized/Open Source): Entry-level emulation using open-source tools like ScadaBR and Unity-based visualization. Useful for foundational training on protocols and attack patterns.
- Layer 2 (Virtualized/Commercial): Commercial virtual software that manufacturers use to test deployments before pushing to physical appliances. This provides more accurate protocol behavior and system responses.
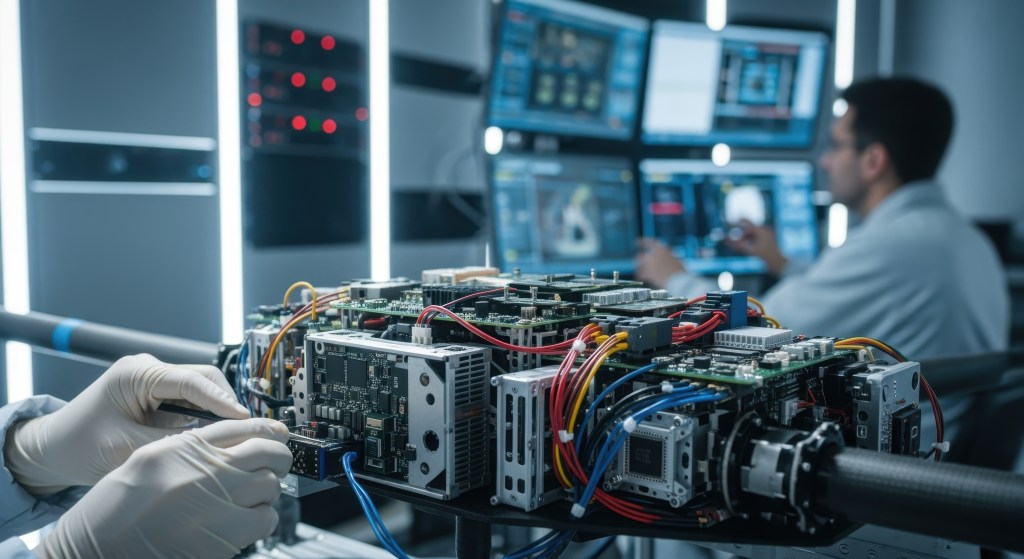
- Layer 3 (Physical/Mini): Here’s where testing crosses from digital simulation into physical reality. Mini hydro kits and electrical training setups that can be integrated directly into the range allow defenders to observe how real machinery responds to malicious commands—not how software approximates that response.
- Layer 4 (Physical/Commercial): Actual hardware components from customer sites integrated into the testing environment. This is the highest fidelity available: defenders train and test on exact replicas of their production equipment, building muscle memory on the systems they’ll actually operate during an incident.
On-Premises Deployment: Behind the Fence Line
For organizations with air-gapped requirements, SimSpace supports full on-premises deployment. The platform runs on private VMware infrastructure—not dependent on AWS, Azure, or GCP—which means sensitive network data never leaves the facility. This “cyber range in a box” approach allows organizations to conduct destructive scenario testing on replicated environments without risking production systems or exposing configuration data to external networks.
Because the platform operates behind existing security boundaries, teams can run live-fire exercises that would be impossible—or unacceptably risky—with cloud-dependent tools. A water utility can simulate a Volt Typhoon–style intrusion attempting to manipulate chemical dosing systems. A power company can test how their protective relays respond when an attacker sends spoofed DNP3 commands. A defense contractor can validate that their incident response procedures actually work when confronted with a sophisticated adversary—not just discuss them in a conference room.
The quantifiable output matters, too. Modern cyber ranges generate detailed metrics on detection times, response accuracy, and procedural gaps that translate directly into board-level reporting and regulatory evidence. SimSpace customers have documented measurable improvements including 48% faster breach detection and 45% improvement in attack defense.
Choosing the Right Approach
For CISOs and security leaders evaluating testing platforms for critical infrastructure environments, several questions should guide the decision:
- Does the platform support fully on-premises deployment, or does it require cloud connectivity?
- Can it integrate physical hardware—including legacy OT systems and specialized firmware—into test scenarios?
- Does it respect existing network segmentation and data diode architectures?
- Can it generate the compliance-ready documentation regulators increasingly expect?
The air gap exists for a reason. Security testing should strengthen it, not undermine it.
To learn how SimSpace supports on-premises cyber range deployment for critical infrastructure organizations, schedule a demo.
For elite cybersecurity teams under siege in an AI-fueled threat landscape, SimSpace is the realistic, intelligent cyber range that strengthens teams, technologies, and processes to outsmart adversaries before the fight begins. To learn how SimSpace helps organizations graduate from individual to team and AI model training; test tools, tech stacks, and AI agents; and validate controls, processes, and agentic workflows, visit: http://www.SimSpace.com.